Email is an essential part or our everyday communications. It is also one of the most common methods that hackers use to attempt to gain access to sensitive information. More than 90% of data breaches start with a phishing attack. Phishing uses fraudulent email messages designed to impersonate a legitimate person or organization. They attempt to trick the recipient into downloading harmful attachments or divulging sensitive information, including passwords, bank account numbers, and social security numbers.
Phishing scams can have a number of different goals. They may attempt to:
- Target your cash and payment card data
- Gain control of your computer and local network resources
- Gain access to your University Computing Account and resources
Phishing scams typically attempt to take advantage of you by:
- Delivering file attachments that can infect your computer with harmful software
- Enticing you to click on links to websites that infect your computer with harmful software
- Tricking you into sharing your username and password so hackers can gain access to your network or other sites
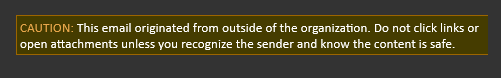
Spotting Suspicious Emails
- Were you expecting an email from this person or organization? If not, this should alert you to the need for some basic visual checks
- Even if the ‘From’ name looks familiar hover your mouse pointer over it to see the email address it came from. Does it look right? If not then do not reply, click on any links within it or open any attachments. Report it to spam@st-aug.edu.
- Similarly, is the email asking you to provide personal information by reply, or click on a link to go to a website, or similar? Again, if you are even slightly suspicious do none of these things, but report it to spam@st-aug.edu.
- Never enter your user name or password into an email asking for them. No legitimate organization or individual will ever ask for this kind of information. If they do, report it to spam@st-aug.edu.
Examples of Suspicious Emails
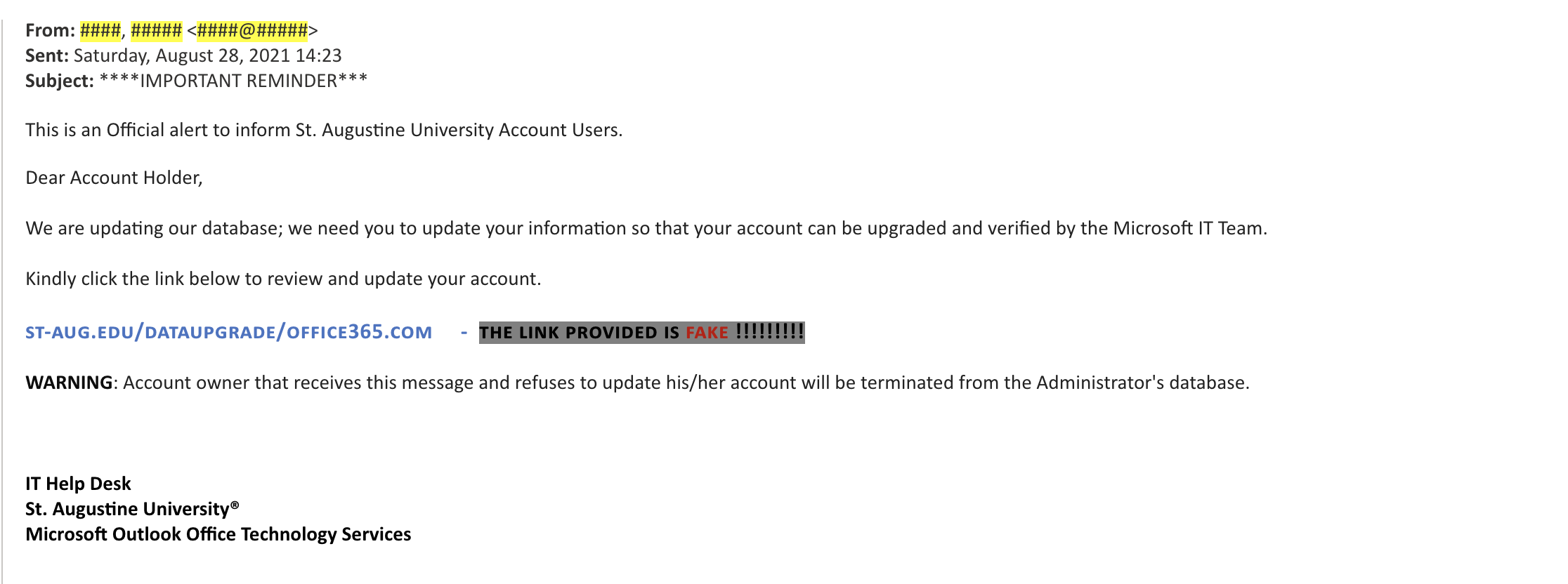
 xyz@gmail.com
xyz@gmail.com
This should make you give pause before opening the Email.
Reporting a Phishing Scam
To report a phishing scam, forward the phishing email as an attachment to spam@st-aug.edu. We will be introducing additional features in the near future to make the reporting process even easier.
Reporting a phishing scam in Microsoft Outlook (Desktop client)
- Select the suspicious email in Outlook.
- Press “Control-Alt-F“. This will open a draft email message with the suspicious email as an attachment.
- Add spam@st-aug.edu in the ‘To:” field of the draft email message.
- Send the email.
Reporting a phishing scam in Microsoft Outlook Online (Office 365)
- Select New to compose a new message.
- In the upper right-hand corner of the new message, click the icon to compose the message in its own window.
- Drag the suspicious email into the body of the new message. This will add the suspicious email as an attachment.
- Add spam@st-aug.edu in the “To:” field of the draft email message.
- Send the email.